 I’d like to expand on Brett’s post a bit with some more recent books that I’ve enjoyed. And another which is perhaps a few clicks off the maintained trail.
I’d like to expand on Brett’s post a bit with some more recent books that I’ve enjoyed. And another which is perhaps a few clicks off the maintained trail.
The Algorithm Design Manual (Steven Skiena)
I’ll kick this discussion off with the fact that I don’t have a Computer Science degree. There, I said it. No degree. Ask me and I’ll give you the info: There’s no Computer Science degree here. Anyway. As a pure practitioner, I love books that usher out-of-reach concepts into the realm of real-world applicability, and this one does exactly that. This book is one part catalog of algorithms, the other part a series of “war stories” — real problems the author has tackled during his career using variations of the algorithms presented.
The Little Schemer (Matthias Felleisen, Daniel P. Friedman)
This book taught me a conscious way to write recursive routines. Prior to reading, I’d hammer the keyboard with a gloved hand and hope for the best. The preface mentions that this book is itself derived from a course taught by the authors on Scheme programming — to non-technical public affairs students. Yes, so you might imagine that the presentation inside is not your typical c0d3rz manual. I’ve dispatched this book to a couple of my non-technical friends, and the consensus is that this book is a gem.
Hacker’s Delight (Henry S. Warren, Jr.)
Count 1-bits in a word. Reverse bits in a byte. Transpose a 32×32 bit matrix. This book is a catalog of interesting passages of low level bit-twiddling code. Thanks to modern day tools, I haven’t needed to reach for many of the tactics described in this book, but it is an enjoyable and mind-contorting swim through the ether of machine words and switch flippery. Looks like I need to pick up the recently released second edition.
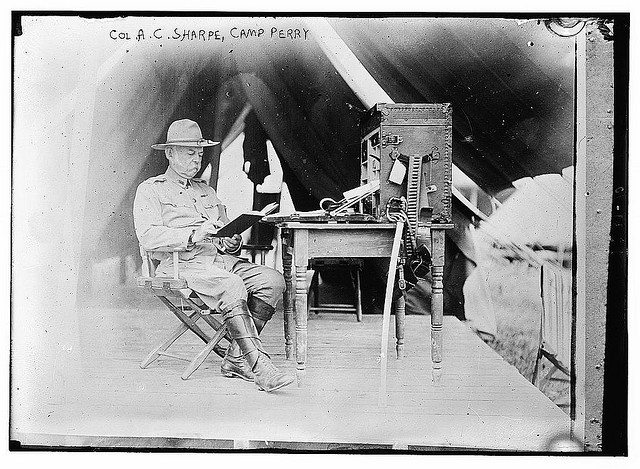
Image via http://www.flickr.com/photos/library_of_congress/2162719777/sizes/z/in/photostream/
Spot the Vulnerability: Loops and Terminating Conditions
Spot the Vulnerability: Loops and Terminating Conditions In memory-unsafe languages like C, special care must be taken when copying untrusted data, particularly when copying it to another buffer. In this post, we\'ll spot and mitigate a past vulnerability in Linux\'s...


