On a recent Tuesday night tapas meet-up, my friend and I were talking about social media and her use of it. She had been studiously avoiding it in an effort to keep her online profile low. I countered with my usual “that ship has sailed” speech: She has a Gmail account, uses Google, debit and credit cards, club and membership cards, etc. Her eyes grew wide in disbelief and she launched into a somewhat predictable reaction of fear, loathing and righteous indignation over the violation of her privacy.
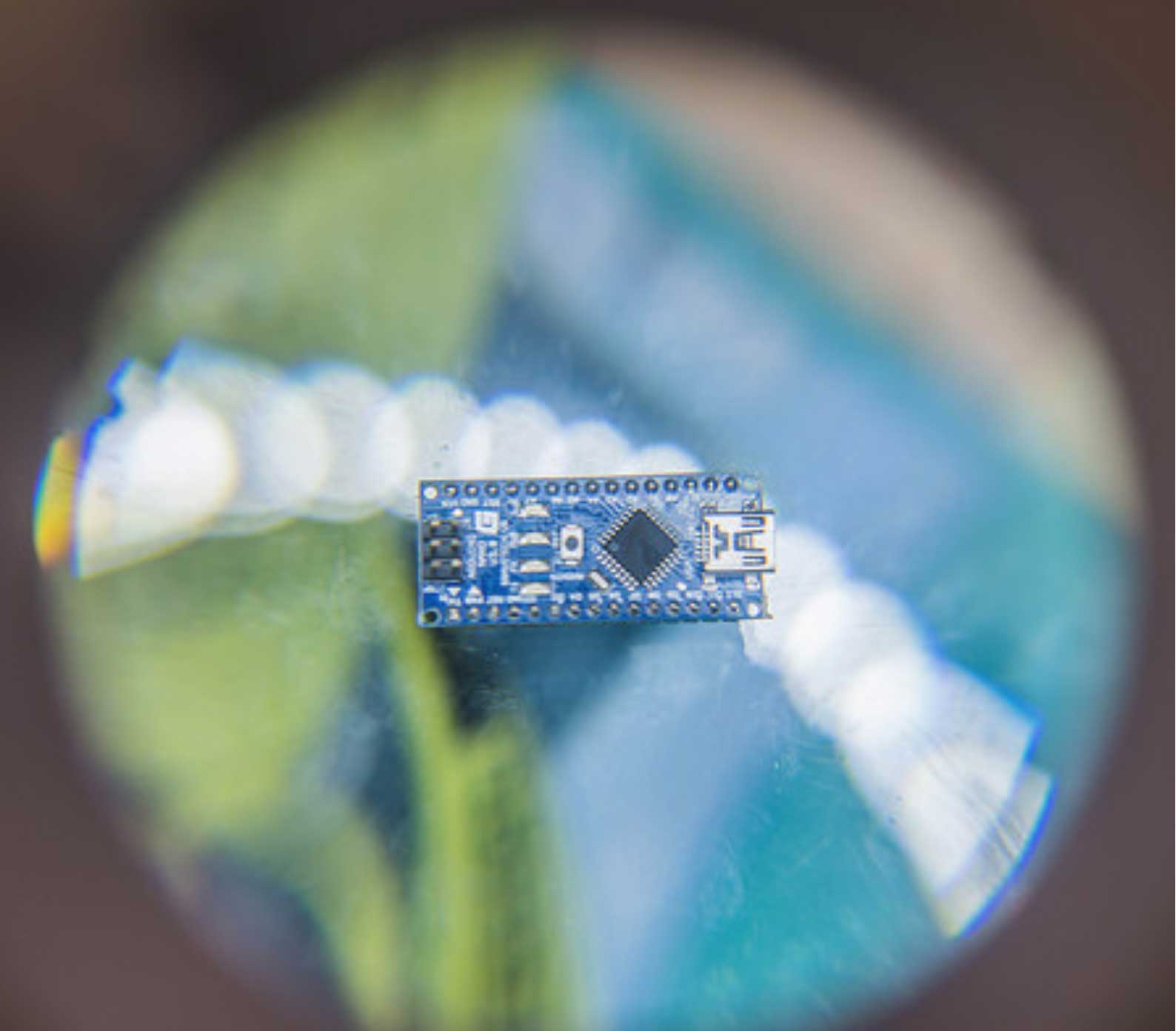
I sighed and began to talk about technology, how and why we use it, Big Data and the Internet of Things, which may not have been the smartest of moves, but was fueled by our solid friendship and the arrival of miniature plates of mussels, crostini, and warmed olives.
I can’t help it. I am authentically interested in how new technology moves from the academic to the novel to the ubiquitous over time and I’ve been a spectator of that evolution for over a decade.
When I speak with a potential client, I see this migration made manifest. I may, early on, speak only rarely with clients looking to use a new technology and frequently the discussions feel fumbling and vague. If the project moves into implementation, the development of the application may be far more iterative than normal, simply because we are in uncharted waters. No one quite knows how the users are going to respond or what they will do. It’s sort of like playing with a new toy. From my perspective, these projects can be thrilling and surprising. Making applications that run on new devices or use new technologies is like witnessing the future; I remember the first iOS application we developed (which premiered with the opening of the AppStore), the first responsively designed website, the first application created using 3D camera technology, the elegance of the newer JavaScript libraries. We are currently writing an application using some cutting-edge Windows tools and, at a recent demo, I got a little verklempt. It was so astounding.
As time passes, however, I have more and more discussions about a new device or technology. It fills my daily life. Everyone wants to do something with that technology or device – users are expecting the experience or functionality that they provide.
At the 2016 CES show, IoT (Internet of Things) was represented, in large part, by toys. As well it should be. This often seems to be how new devices and technologies are introduced and adopted. In the beginning, with mobile devices, we saw them being leveraged for social media and applications that were novelties or game/entertainment-centric. Over the next few years, I saw a marked increase in the sophistication of iOS applications – in their UX, in their features, and in their intended use. Currently, we are developing mobile applications that serve as keystones to robust enterprise solutions. As a population, we’ve discovered how to use IoT tools and, more importantly, we’ve culturally made the leap that allows users to accept these devices as part of our lives. We’ve gone from early-adopter techies to great-grandparents. We’ve moved from gimmicks and toys to enterprise solutions. Mobile devices are integrated into our schools and our workplaces and I do believe that this is only the beginning of their story in our lives.
IoT is a big thing now. It has that cute little TLA (Three Letter Acronym) with the lower-case “o”. It sounds new and novel (Although, as I pointed out to my dinner-mate, that thing sitting to the right of her wine glass is a Thing. She looked at it like it had just turned into a cockroach.) But I am very interested to see where that TLA takes us, what its story will be in our lives. I am interested in watching it migrate from fear and loathing to acceptance and pervasiveness. What projects related to that journey will we be doing? I know that part of that cultural hill to climb is that we need to become accustomed to data collection devices doing just that – constantly collecting data about us and providing an interface by which to access that data. We also likely need to become accustomed to sharing that data broadly so that the data collected by those Things can be used to drive insight and accuracy.
It is, perhaps, because of my own personal history with medical devices that I’m more comfortable with this concept than most. Before my pancreatic transplant, and as a Type-1 diabetic, I spent every day tethered to multiple devices. And those devices had interfaces that allowed the data they collected to be downloaded to software programs that, in turn, allowed me to understand trends and patterns that I could then share with my physician who was able to offer his feedback. This approach allowed us to create a finely tuned care plan.
Currently, I use other devices to monitor my daily health but I find them limited – mostly in that they aren’t integrated and/or real-time. Integration and real-time are where the functionality really takes a leap. It further takes a leap when the integration and real-time data of one device can be married with multiple devices.
What I told my friend, to her horror, was that I looked forward to the day my whole house is a series of connected Things, collecting data, processing data and then sharing that data back out to me and to my physicians and to researchers. I want my bed to report on my sleep, I want my bathroom floor to report on my weight. I want my toilet to test for glucose, creatinine, protein, a slew of other abnormalities and calculate if I’m dehydrated. I want my refrigerator to map my calorie consumption and the types of calories I am consuming, roughly, and yes, I want it to prepare a shopping list I can edit, add to and approve and then send to the Hannaford’s for processing and pick up. I want my medication bottles to capture when I take my medication and alert me when it appears I’ve missed a dose. And I want the whole lot, along with my FitBit data, to be presented to me on my personal profile with filterable graphs and bells and unicorns!
And this is where I expect I’ll see the new, tentative wave of entrepreneurs appearing in my world. This is, for us, the next wave of development. Not so much with the devices and the software that directly supports them, but in the software that pulls disparate data streams together and provides unique slices of insight to the user based upon specific objectives. It’s in the daisy-chaining of services, not the services themselves, where I see my future client conversations happening.
And Bio-Med is a single industry where this makes a good deal of sense, but I see similar futures for Manufacturing, Education, Finance, and Compliance.
At this point, my friend tossed aside a mussel shell.
“Look,” she said, “I don’t want my toilet calling my pharmacist.”
I raised an eyebrow, teasing her. “You say that now. I’ll remind you of this moment when we’re standing in the Home Depot eight years from now debating whether or not to get the SmartiePottie™ in bisque or white…”
Spot the Vulnerability: Loops and Terminating Conditions
Spot the Vulnerability: Loops and Terminating Conditions In memory-unsafe languages like C, special care must be taken when copying untrusted data, particularly when copying it to another buffer. In this post, we\'ll spot and mitigate a past vulnerability in Linux\'s...