In my last post, I created a visualization of where information is hidden in an image using a steganographic tool called PixelJihad. In this post, I’ll talk about a rudimentary method of searching for the pixels that may be hiding information. This is our first stop on the path to evaluating whether the image may contain hidden information.
PixelJihad takes the message, optionally encrypting it, and scatters the data throughout the image using a deterministic function based upon the password provided. The expectation is that this will look like noise on the image and remain unnoticed. As I noted in the last post, there are ways to analyze images to detect such patterns. The difficulty lies in doing this efficiently.
I’ve modified the PixelJihad tool to read all the pixels of an image and provide a visual analysis that illustrates pixels whose channels do not substantially match the neighboring pixels. In the red channel of a pixel does not have the same value as the majority of its neighboring pixels’ red channels, a red pixel is drawn on the image map. To remove real noise from the image, any pixel where more than one channel is substantially different from that of the neighboring pixels has been ignored.
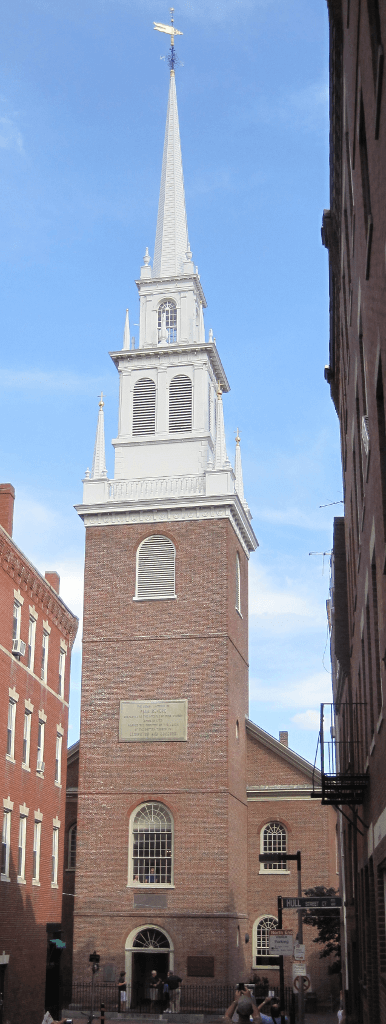
I’ve taken a scaled-down copy of this photograph of the Old North Church (by Teemu008) and embedded a stanza from “Paul Revere’s Ride” with the password “Henry Wadsworth Longfellow”. (The phrase I used in the last post was too small to have a substantial impact on the data in the image.)
Here’s the scaled-down photograph:
Here’s the analysis of that photograph:
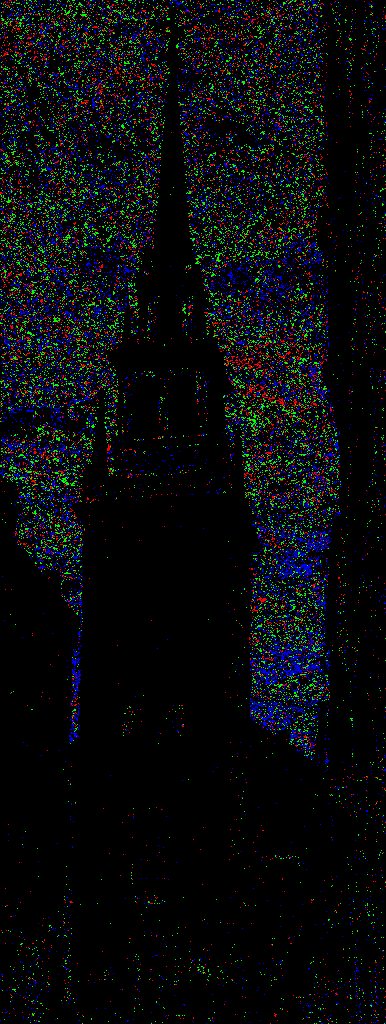
Here’s the analysis of the photograph with the hidden message:

There isn’t much of a visible difference. Unfortunately, this method (which works very nicely on images with areas of one color) does not work well on photographs. As you can see, a photograph of a cloudy sky is a great place to hide information using the PixelJihad tool. (Unfortunately, the PNG format does not handle such images efficiently.)
Can you think of a better way to detect hidden information in these images? Take a look at my code and let me know in the comments.
Spot the Vulnerability: Loops and Terminating Conditions
Spot the Vulnerability: Loops and Terminating Conditions In memory-unsafe languages like C, special care must be taken when copying untrusted data, particularly when copying it to another buffer. In this post, we\'ll spot and mitigate a past vulnerability in Linux\'s...


