Spot the Vulnerability: Data Ranges and Untrusted Input
In 1997, a flaw was discovered in how Linux and Windows handled IP fragmentation, a Denial-of-Service vulnerability which allowed systems to be crashed remotely.

Common Sense Security Tips to Protect Your Computers and Devices
If you want to make yourself too anxious to sleep at night, take a security expert out to lunch and ask about all of the ways in which your personal information is vulnerable at home, work, and on the internet. It will be an eye-opening experience! You’ll hear about encryption standards, key management, multi-factor authentication, SQL injection, DDoS attacks, men in the middle, attack vectors, AppSec, OWASP, Pen Tests, social engineering, black hats, white hats, grey hats and one hundred different terrifying data breaches (Target, Sony, Anthem, Home Depot and the like). Here’s some advice on how to protect yourself.
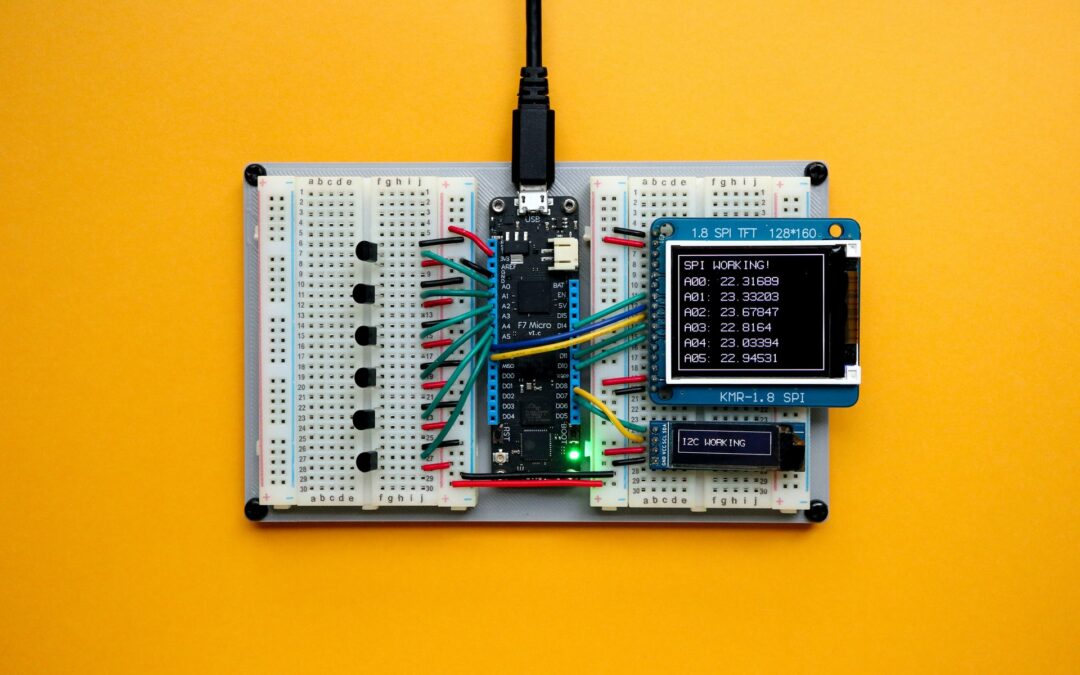
Security and the Internet of Things (IoT)
Are you thinking about the Internet of Things (IoT)? Maybe you should be — a whole new class of devices with previously unthought of capabilities is beginning to appear on the market. Corporate juggernauts and lean startups can both play the game, with home and...