
Accurate Timing
In many tasks we need to do something at given intervals of time. The most obvious ways may not give you the best results. Time? Meh. The most basic tasks that don’t have what you might call CPU-scale time requirements can be handled with the usual language and...
Bringing an Idea to Life: WatchWah Proof of Concept
How do you get from a great idea to a product? Start with a quick proof-of-concept. This project sets out to determine whether or not the Apple Watch can control a guitar effect, and add a little Jimi Hendrix to my tone.
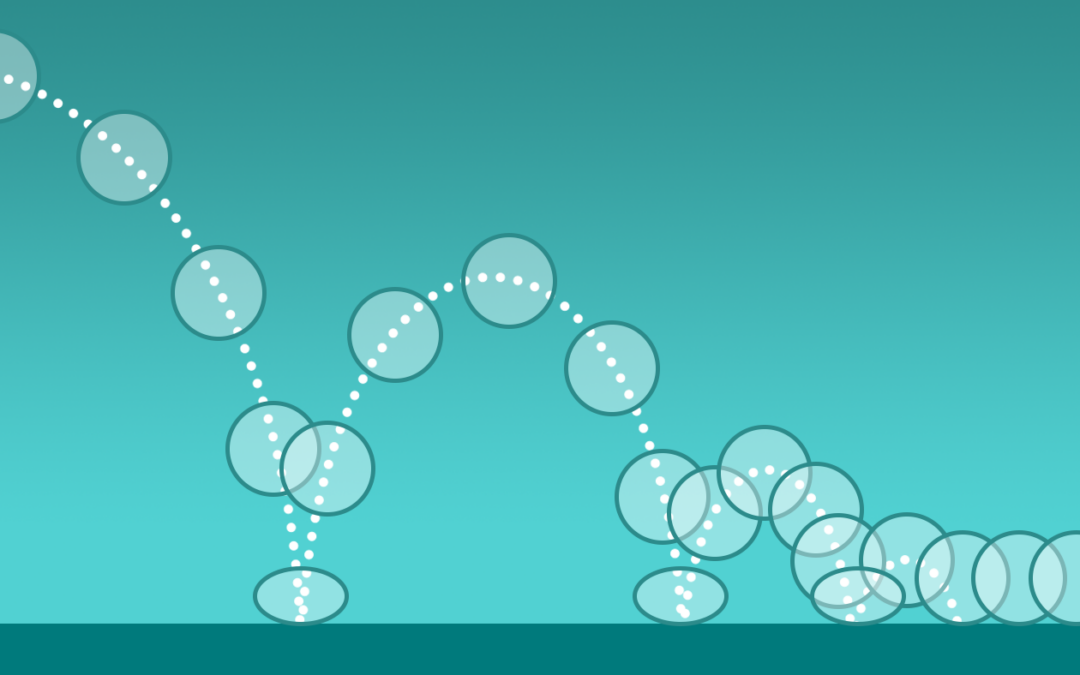
Re-animated
Recently, I spent a bit of time updating the `friz` animation control framework for JUCE that I wrote last year, adding a few things to it that make it easier to use and more expressive.